In today’s heterogeneous environments, you collect logs from a variety of sources and forward them to multiple destinations, which often requires special purpose agents. The need to maintain a large number of logging agents creates operational complexity and costly overhead, and updating, maintaining and configuring these agents is a time-consuming activity. View this webcast to learn how the log collection […]
Read more ›Articles By: syslog-ng

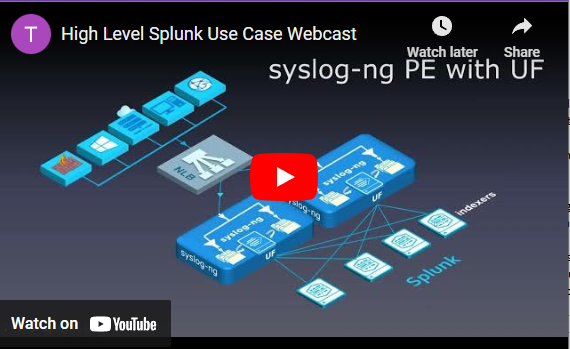
White Paper: How to Configure Syslog-Ng™ PE to Cooperate With Splunk
Splunk is a popular search and analysis platform. Many users of Splunk also have syslog-ng™ deployed in their environments. This guideline describes scenarios in which Splunk users can benefit from syslog-ng™ Premium Edition features and offers some technical guidance to optimize the syslog-ng™ configuration. Read this guide to see five use cases, including:• Collecting logs from network devices• Feeding multiple […]
Read more ›
The 1m+ EPS UDP Ingestion Challenge
Even in 2019, many organizations rely on UDP to ship syslog messages from endpoints to Splunk where TCP transport is either not feasible or desirable. Scaling UDP ingestion with no message loss is far from a trivial task. Join us for our on-demand webcast which will showcase how you can achieve 1m+ EPS UDP ingestion with a single syslog-ng instance […]
Read more ›
How to use the syslog-ng PE’s new Google Stackdriver destination
Google Stackdriver is a flexible and convenient way to monitor and manage your cloud-based assets, regardless of where they are located or how they are configured. If your organization is completely in the cloud, has apps on Google Cloud or Amazon Web Services, or if you manage a hybrid environment, Stackdriver is a terrific solution. Join this on-demand webinar, hosted […]
Read more ›
Five Things Every Business Needs to Know About GDPR
RE-EXAMINE YOUR PROCEDURES AND ENSURE COMPLIANCE After years of preparation and drafting, the final t’s were crossed and i’s dotted on the General Data Protection Regulation (GDPR), when the Council of the European Union and the European Parliament adopted it. It means that it’s time to stop thinking about GDPR and to start acting. Particularly as they will have less […]
Read more ›
NIST Cybersecurity Framework
The second function within the framework entitled “Protect”, places great emphasis on managing privileged authorized user access to critical assets. In order to manage and supervise connections to critical assets, organizations commonly invest in some form of access monitoring technology. This paper describes: • How to secure critical assets from unauthorized users and access control authorized users. • How to […]
Read more ›
Optimizing SIEM
Security Information and Event Management (SIEM) solutions form the core of many organizations’ security strategy, but SIEMs can be expensive, eat up storage and get overwhelmed by the amount and number of formats of log data that they need to process. But there is a way to optimize the performance of your SIEM solution that can make your organization more […]
Read more ›
Upgrade to State-of-the-Art Log Management
MAKE THE MOST OF YOUR INVESTMENT Most log messages traditionally come from three types: system logs of servers, network devices, and applications. To derive actionable, valuable business information from this vast amount of raw log data, it is necessary to collect, filter, and normalize messages from various sources and store them centrally so that they may be easily accessed for […]
Read more ›