The uncertainty surrounding the global pandemic has highlighted the urgent need for organizations to not only better understand their customers, but also meet and exceed customer expectations. Customer support teams in particular now have the perfect opportunity to get personal in today’s digital age by leveraging technology to transform customer relationships. Intercom commissioned Forrester Consulting to conduct a survey which […]
Read more ›
GigaOm Radar for Phishing Prevention and Detection
Email remains a leading conduit for malware delivery and phishing exploits. According to the GigaOm Radar for Phishing Prevention and Detection, an effective anti-phishing solution must be a critical component of your enterprise security strategy. Multiple areas evaluated by GigaOm in this independent analyst report include: Download the ebook now to learn:• Target market segments — Small/Medium Enterprise, Large Enterprise, […]
Read more ›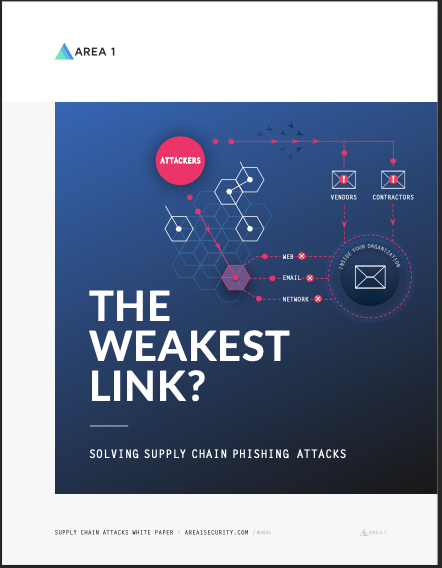
The Weakest Link? Solving Supply Chain Phishing Attacks
Hackers have goals. Whether the goal is to steal data or funds, or to cause physical destruction, they will seemingly stop at nothing to get what they want. The easiest — and least detectable — method is to compromise your third-party vendors and suppliers, instead of your organization directly. Supply chain attacks increasingly threaten organizations — a risk made frighteningly […]
Read more ›
Phishing with the Cloud: One Million Ways Attackers Breach Office 365 Email
Download your copy of “Phishing with the Cloud: One Million Ways Attackers Breach Office 365 Email” now to learn: • The types of phishing campaigns most frequently missed by Office 365’s email defenses• Real examples of Business Email Compromise, brand spoofs and other phishing threats that evade Office 365• What makes Office 365 (even if combined with SEGs and DMARC) […]
Read more ›
PHISHING AND THE MITRE ATT&CK FRAMEWORK
Download your copy of “Phishing and the MITRE ATT&CK Framework” now to learn:• How comprehensive email security can be mapped to the MITRE ATT&CK framework• A breakdown of example malware phishing mapped to the MITRE ATT&CK framework• The importance of anti-phishing to preempt damages caused by malware, ransomware, Types 1 – 4 Business Email Compromise (BEC) and other threats
Read more ›
Office 365, Compromised On-demand Webinar
So far this year, Area 1 has intercepted $273 MILLION+ in active Business Email Compromise — phishing attempts that were missed by Office 365, email gateways and other traditional defenses. Even with ATP, if you’re missing a purpose-built, cloud-native email security layer, your Office 365 users are at risk for Business Email Compromise phishing and other advanced threats. Watch this […]
Read more ›
Business Email Compromise in 2021: Supply Chain-based Phishing Attacks on the Rise
Here is your complimentary copy of Business Email Compromise in 2021: Supply Chain-Based Phishing Attacks on the Rise. Most organizations aren’t equipped to stop Business Email Compromise (BEC) phishing – particularly the new, third and fourth generations of BEC attacks that use social engineering to compromise your supply chain. Download the ebook now to learn:• The differences between Types 1, […]
Read more ›
UKG Leads in Usability and Functionality, Says Latest HCM Tech Value Matrix
Of the 16 human capital management (HCM) providers evaluated by Nucleus Research in its 2021 HCM Technology Value Matrix, two UKG solutions — UKG Pro™ and UKG Ready™ — have been named leaders. The designations are based on Nucleus’ assessment of relative usability and functionality of the solutions as well as the value customers have gained from each product’s capabilities. […]
Read more ›