Cloud-native architecture is built upon four pillars:• rapid release cycles,• architectural flexibility,• packaged delivery,• and continuous deployment. These traits have enabled organizations to design and deploy hundreds to thousands of solutions across the world with many other companies hungry to hop onto the cloud-native train. These solutions have helped some of the world’s most forward-thinking enterprises expedite what they can […]
Read more ›
Business Process Management in the Digital Era
Digital enterprises, employing artificial intelligence, cloud, and data analytics in innovative ways, are delivering superior customer experiences, faster response times, and more intelligent operations. Every company—no matter how large, how old, or in what industry—can potentially evolve into a digital enterprise, operating with the same agility of a startup. The only way to advance and compete is to open up […]
Read more ›
Data-Intensive Intelligent Applications in a Hybrid Cloud Blueprint
Data-intensive intelligent applications play a key role in helping organizations provide personalized user experiences to stay competitive. The stages in the life cycle of these applications need to be connected in dispersed deployment environments, potentially spanning multiple cloud providers, in-house datacenters, and edge devices. Red Hat provides the methodology and technology required to build, maintain, and manage these complex hybrid […]
Read more ›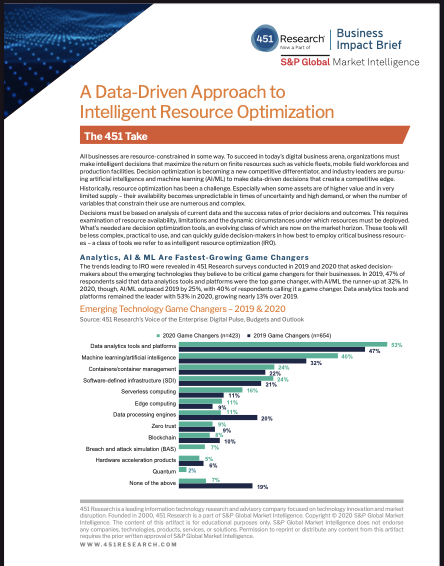
A Data-Driven Approach to Intelligent Resource Optimization
451 Research found that analytic platforms, artificial intelligence, and machine learning have become a top priority for organizations. Learn why.
Read more ›
451 Research: The Role of AI in Automating Processes and Decisions
In this Pathfinder report, 451 Research shows how to use intelligent process automation to improve decision making and business process management. The research found that 79% of respondents have AI strategies, which include plans to automate various business functions. Intelligent automation technology empowers business experts to build and enforce rules and policies throughout the enterprise application stack. This approach allows, […]
Read more ›
Building a Culture of Connection to Drive Team Engagement
How connected, dynamic teams drive success in the new world of work As organizations adapt to rapidly changing business environments, getting the right team with the right people with the right skills – whether employees or contractors – drives team engagement and productivity. Enabling your leaders to build a team culture and create connection among people working from anywhere is […]
Read more ›
Preparing for Attacks that Seek Total Annihilation
Defending your IT infrastructure against attack has never been a simple task. But things have taken a decidedly ugly turn of late: More and more attacks are simply seeking the total annihilation of your infrastructure. Any organization can be a target – or simply collateral damage from an attack targeting someone else. Sadly, many organizations are simply unprepared, and as […]
Read more ›
Top 10 Active Directory Security Reports and Alerts You Need
The statistics are staggering: 95M Active Directory accounts are attacked every day and 1.2M Azure AD accounts are compromised each month. On top of that, malicious insiders are eagerly looking for data to steal, and stressed-out workers and admins are making careless mistakes. You simply can’t afford to spend hours scouring AD audit logs and taking the very real risk […]
Read more ›