For successful businesses, the Accounting department is the operational backbone, delivering insights to help leaders understand where the company stands, what — if any — changes need to be made, and what the past can tell them about the future. To get to that point, however, Controllers need to walk a tightrope between ensuring sound tactics and building a strategic […]
Read more ›
Controller’s Guidebook – When Accountants Dare to Dream
The talent crisis and constant pressure to do more with less have accounting departments in flux, and an uncertain economic environment is exacerbating these pain points. In the fourth installation of Controller’s Guidebook, FloQast, in partnership with the University of Georgia, invited a diverse group of accountants to dream about how the profession might be different if they were in […]
Read more ›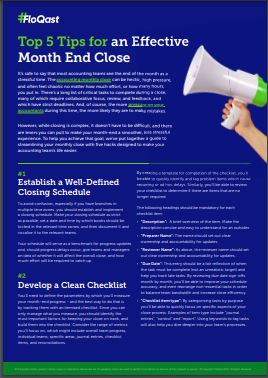
Top 5 Tips for an Effective Month End Close
It’s safe to say that most Controllers see the end of the month as a stressful time. The accounting monthly close can be hectic, high pressure, and often feel chaotic no matter how much effort–or how many hours–you put in. Closing can be complex, but it doesn’t have to be difficult. You can make your month-end smoother and less stressful […]
Read more ›
Controller’s Guidebook – Burnout in Accounting
Burnout in the accounting profession has been measured with academic approaches never-before-applied in the industry. FloQast, in partnership with the University of Georgia, analyzed survey data from a diverse group of accounting professionals to understand what’s causing burnout, how it impacts both business outcomes and personal lives, and what steps can be taken to create a roadmap for the future.
Read more ›
It’s More Than Just ChatGPT: The Role of AI and ML in Talent Selection
When you think about artificial intelligence (AI) and machine learning (ML), what comes to mind? If it’s ChatGPT, AI-generated art, and autonomous pizza delivery, you’re not alone. These are just a few of the most buzzworthy developments in AI and ML from the past few years–and they’re just the tip of the iceberg. Download this guide to learn all about […]
Read more ›
Top 20 Tech Recruiting Platforms to Supercharge Your Hiring
Digital transformation has led to a surge in demand for skilled technical talent, not just in tech companies, but across various sectors including finance, healthcare, retail, and government. Additionally, advancements in artificial intelligence (AI), like ChatGPT, are reshaping the skills required and the methods used for assessing software engineering talent. Hence, recruiters and hiring teams need the right platforms and […]
Read more ›
CFO’s Guide to AI
We asked ChatGPT, “Can you tell me 5 things to watch out for when accounting for intercompany transactions?” and followed up with “What steps should I take to ensure my company is ASC 842 compliant?” Its answers are instructive for companies considering adopting AI and machine learning techs — and for those that are not. Download our guide to see […]
Read more ›
Metrics That Matter
We’ve all heard the truism that “what gets measured gets managed.” With data more accessible and easier to track than ever, you have the opportunity to both measure and actively manage all aspects of the business. So why are leaders still lamenting a lack of data insights? Address that by democratizing data and metrics, including using an objectives and key […]
Read more ›